Cyber Security Training by Experts
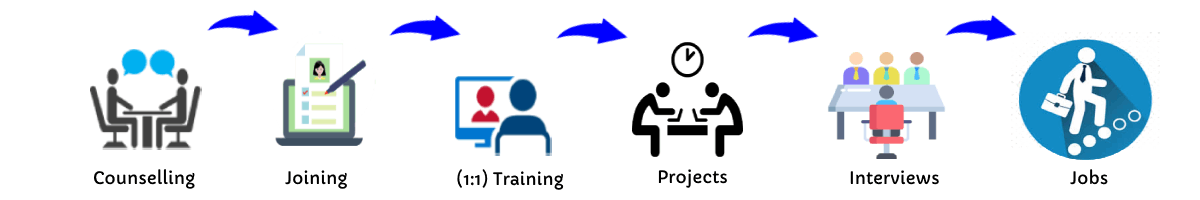
Our Training Process
Cyber Security - Syllabus, Fees & Duration
MODULE 1
- Cyber security
- Importance and challenges of cyber security
- Integrity, availability
- Layers of cybersecurity
MODULE 2
- Types of Malware
- Worms
- Viruses
- Spyware
- Trojans
MODULE 3
- Cyber security fundamentals
- Cyber criminology
- Cyber forensics
MODULE 4
- Cyber security breaches
- Phishing
- Identity Theft
- Harassment
- Cyber stalking
MODULE 5
- Types of cyber-attacks
- Web-based attacks,
- System-based attacks
- Password attack
- Passive attacks
- Denial of service attacks
MODULE 6
- Prevention tips
- Craft a Strong Password
- Two Step Verification
- Download Attachments with Care
- Question Legitimacy of Websites
MODULE 7
- Mobile protection
- No Credit Card Numbers
- Place Lock on Phone
- Do not Save Passwords
- No Personalized Contacts Listed
MODULE 8
- Social network security
- Do not Reveal Location
- Keep Birthdate Hidden
- Have Private Profile
- Do not Link Accounts
MODULE 9
- Prevention software
- Firewalls
- Virtual Private Networks
- Anti Virus and Anti Spyware
- Routine Updates
MODULE 10
- Critical cyber threats
- Cyber terrorism
- Cyber warfare
- Cyber espionage
MODULE 11
- Defence against hackers
- Cryptography
- Digital Forensics
- Intrusion Detection
- Legal Recourse
MODULE 12
- Wrapping up
- Words from the Wise
- Review of Parking Lot
- Lessons Learned
- Completion of Action Plans and Evaluations
This syllabus is not final and can be customized as per needs/updates




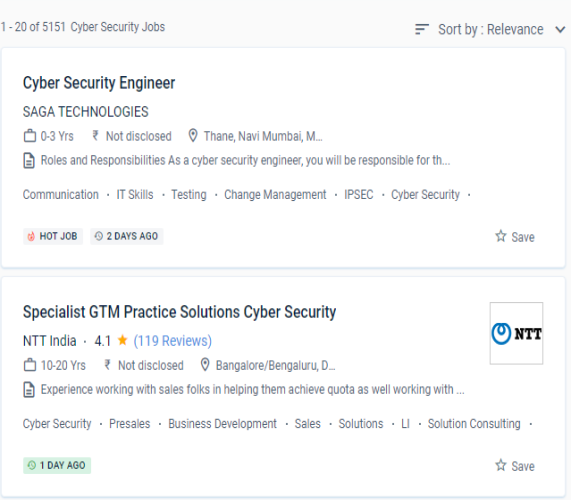
 These courses can help you gain a better grasp of cybersecurity best practices in business settings, such as how to undertake digital forensics, risk analysis, and vulnerability assessments. Any cyber-attack that concerns information security and, in some cases, national security, including electronic systems, personal information, backup copies, and so on.
Cyber-attacks are becoming more widespread, and antivirus software is no longer sufficient. For example, experience with everything connected to access control, security strategies, network risk assessment, and so on is required for this position. Learn how to defend network infrastructures, detect threats, and deploy security solutions, as well as other aspects of computer security. As more devices become Internet-enabled and more services go online, the topic of computer security has exploded.
To begin with, when it comes to protecting a company's or an individual's valuable resources, cybersecurity is the first line of protection.
If you enjoy programming and problem solving, as well as a fast-paced and challenging career, cybersecurity may be a good fit for you. In terms of the business case, cybersecurity protects the company's assets from breaches in its information systems, personal data, and mobile devices. Cyber security is a serious matter, and businesses invest a lot of money to guarantee that their computer systems are secure.
These courses can help you gain a better grasp of cybersecurity best practices in business settings, such as how to undertake digital forensics, risk analysis, and vulnerability assessments. Any cyber-attack that concerns information security and, in some cases, national security, including electronic systems, personal information, backup copies, and so on.
Cyber-attacks are becoming more widespread, and antivirus software is no longer sufficient. For example, experience with everything connected to access control, security strategies, network risk assessment, and so on is required for this position. Learn how to defend network infrastructures, detect threats, and deploy security solutions, as well as other aspects of computer security. As more devices become Internet-enabled and more services go online, the topic of computer security has exploded.
To begin with, when it comes to protecting a company's or an individual's valuable resources, cybersecurity is the first line of protection.
If you enjoy programming and problem solving, as well as a fast-paced and challenging career, cybersecurity may be a good fit for you. In terms of the business case, cybersecurity protects the company's assets from breaches in its information systems, personal data, and mobile devices. Cyber security is a serious matter, and businesses invest a lot of money to guarantee that their computer systems are secure.